Learn about cyber security, why it's important, and how to get started building a cyber security program in this installment of our Data Protection 101 series.
A DEFINITION OF CYBER SECURITY
Cyber security refers to the body of technologies, processes, and practices designed to protect networks, devices, programs, and data from attack, damage, or unauthorized access. Cyber security may also be referred to as information technology security.
THE IMPORTANCE OF CYBER SECURITY
Cyber security is important because government, military, corporate, financial, and medical organizations collect, process, and store unprecedented amounts of data on computers and other devices. A significant portion of that data can be sensitive information, whether that be intellectual property, financial data, personal information, or other types of data for which unauthorized access or exposure could have negative consequences. Organizations transmit sensitive data across networks and to other devices in the course of doing businesses, and cyber security describes the discipline dedicated to protecting that information and the systems used to process or store it. As the volume and sophistication of cyber attacks grow, companies and organizations, especially those that are tasked with safeguarding information relating to national security, health, or financial records, need to take steps to protect their sensitive business and personnel information. As early as March 2013, the nation’s top intelligence officials cautioned that cyber attacks and digital spying are the top threat to national security, eclipsing even terrorism.
CHALLENGES OF CYBER SECURITY
For an effective cyber security, an organization needs to coordinate its efforts throughout its entire information system. Elements of cyber encompass all of the following:
Network security
Application security
Endpoint security
Data security
Identity management
Database and infrastructure security
Cloud security
Mobile security
Disaster recovery/business continuity planning
End-user education
The most difficult challenge in cyber security is the ever-evolving nature of security risks themselves. Traditionally, organizations and the government have focused most of their cyber security resources on perimeter security to protect only their most crucial system components and defend against known treats. Today, this approach is insufficient, as the threats advance and change more quickly than organizations can keep up with. As a result, advisory organizations promote more proactive and adaptive approaches to cyber security. Similarly, the National Institute of Standards and Technology (NIST) issued guidelines in its risk assessment framework that recommend a shift toward continuous monitoring and real-time assessments, a data-focused approach to security as opposed to the traditional perimeter-based model.
MANAGING CYBER SECURITY
The National Cyber Security Alliance, through SafeOnline.org, recommends a top-down approach to cyber security in which corporate management leads the charge in prioritizing cyber security management across all business practices. NCSA advises that companies must be prepared to “respond to the inevitable cyber incident, restore normal operations, and ensure that company assets and the company’s reputation are protected.” NCSA’s guidelines for conducting cyber risk assessments focus on three key areas: identifying your organization’s “crown jewels,” or your most valuable information requiring protection; identifying the threats and risks facing that information; and outlining the damage your organization would incur should that data be lost or wrongfully exposed. Cyber risk assessments should also consider any regulations that impact the way your company collects, stores, and secures data, such as PCI-DSS, HIPAA, SOX, FISMA, and others. Following a cyber risk assessment, develop and implement a plan to mitigate cyber risk, protect the “crown jewels” outlined in your assessment, and effectively detect and respond to security incidents. This plan should encompass both the processes and technologies required to build a mature cyber security program. An ever-evolving field, cyber security best practices must evolve to accommodate the increasingly sophisticated attacks carried out by attackers. Combining sound cyber security measures with an educated and security-minded employee base provides the best defense against cyber criminals attempting to gain access to your company’s sensitive data. While it may seem like a daunting task, start small and focus on your most sensitive data, scaling your efforts as your cyber program matures.
Saturday, November 11, 2017
Tuesday, November 7, 2017
What is Tunneling?
Tunneling is a method that protects the contents of protocol packets by encapsulating them in packets of a different protocol. Actually, transferring a letter to your grandma includes the use of a tunneling process. You create the personal letter (the primary content protocol packet) and place it in a container (the tunneling protocol). The container is delivered through the postal service (the untrusted intermediary network) to its proposed receiver.
Tunneling can be used in many conditions, such as when you are avoiding firewalls, gateways, proxies, or other traffic control devices. The bypass is accomplished by encapsulating the restricted content inside packets that are authorized for sending. The tunneling process stops the traffic control devices from blocking or filtering the communication because such devices don’t know what the packets really contain.
Tunneling secures the contents of the internal protocol and traffic packets by covering it in an authorized protocol used by the intermediary network or connection. Tunneling can be applied if the original protocol is not routable and to have the entire number of protocols supported on the network to a minimum.
What is Bitcoin? How does it work?
What is Bitcoin?
Bitcoin is a cryptocurrency and a digital payment system created by an unknown programmer, or a group of programmers, under the name Satoshi Nakamoto. It is the first decentralized digital currency.
Bitcoins are digital coins, you can send over the internet. Compared to other choices, bitcoin have many advantages. They are transferred straight from person to another via Internet without going to the bank. It means that the transactions fees are extremely lower, anyone can use them in every country, the account cannot be frozen and there are no limits.
How does it work?
Many currency exchanges exist on the Internet where you can buy and sell bitcoins. Your coins are saved in your digital wallet on your computer or mobile device or any online wallet. Sending and receiving Bitcoins is as easy as sending and receiving email, you can buy anything with Bitcoin.
When it comes to the transaction it generates a first Bitcoin address, something like an email, which acts in a way that they can send you money, by using that address you can use it and receive the Bitcoins in your wallet. You can generate as many addresses as you want, it is best to use them only once.
The bitcoins system is secured by individuals called Bitcoin miners. Workers or miners are paid newly created bitcoins for verifying transactions. All transactions after verified are recorded in a transparent public record.
What is a Jammer?
Signal jammer is created to help people solve different problems coming from cell phones, radio signals and wireless connections. Every kind of signal jammer is designed to work with a specific frequency range.
For example, WiFi signal jammer has been created to successfully block wireless signals in WiFi frequency range (2.4-2.5 GHz) and in addition, it blocks Bluetooth signals because the match the same frequency range. Everything else in this type of jammer works the same as in other jammers, maybe with some minor differences.
Jamming is regularly recognized from interference that can happen due to device defects or other accidental events. Devices that easily cause interference are regulated under various regulations. Jamming happens when an operator transmits on a busy frequency without first checking whether it is busy, or without being able to hear stations using the frequency.
There are some techniques to identify and stop these sorts of attacks. Wireless intrusion prevention systems (WIPS) can make the signal jammer apparent, WIPS is a network device that monitors the radio spectrum for the presence of unauthorized access points (intrusion detection), and can automatically take countermeasures (intrusion prevention). Some radio-based devices support spread spectrum modulation so that hardware can cycle through different frequencies to make the devices harder to jam.
Man in the middle attacks tutorial
MITM attacks (Man -In-The -Middle )
MITM are attacks where the attacker places themself between a “victim machine” and the “router”, this generally occurs without the knowledge of the victim.
A MITM attack exploits the real-time packets in transit allowing attackers to intercept, send and receive data never meant to be for them without either outside party knowing until it is too late.
Disclaimer – Our tutorials are designed to aid aspiring pen testers/security enthusiasts in learning new skills, we only recommend that you test this tutorial on a system that belongs to YOU. We do not accept responsibility for anyone who thinks it’s a good idea to try to use this to attempt to hack systems that do not belong to you
Victim IP address : 1.0.0.98
Router IP address : 10.0.0.1
Requirements:
1. Arpspoof
2. Driftnet
3. Urlsnarf
Open your terminal and configure your Kali Linux machine to allow packet forwarding, because Kali Linux must act as router between “real router” and the victim.
first step is setting up arpspoof between victim and router.
# sudo arpspoof -i eth0 -t 1.0.0.98 10.0.0.1
And then setting up arpspoof to capture all packet from the router to the victim machine .
# sudo arpspoof -i eth0 10.0.1.1 10.0.1.98
now all the packet sent or received by the victim should be going through the attacker machine.
as an exemple we will capture image trafic , so we need to use drifnet Driftnet ( is a program which listens to network traffic and picks out images )
to run drifnet just type :
# sudo driftnet -i eth0
when the victime browse a website with images , drifnet will capture all images trafic .
this is the victime machine while browsing images
and driftnet will capture all image traffic as shown in the screenshot below.
Ubuntu vs Linux Mint : Which Distro Should You Use?
Ubuntu and Linux Mint are both famous for being very friendly for beginners. Ubuntu is the most popular Linux distro and Linux Mint is based on Ubuntu. But there are some real differences between both of these. And how would you choose the one for you? today we will answer this Ubuntu vs Linux Mint question.
System Requirements
Linux Mint:
512MB Ram with 1GB as recommended.
9GB of disk space with 20GB as recommended.
800 x 600 screen resolution with 1024 x 768 recommended.
Ubuntu:
512MB RAM with 2GB as recommended.
5GB of disk space with 25GB as recommended.
1024 x 768 screen resolution.
Interface
Most distros opt the standard Linux desktop interface as their default. But Both Linux Mint and Ubuntu developed their own.
Ubuntu makes use of the Unity interface. Unity Interface is a GNOME-based desktop environment that is common only to Ubuntu. To say simply, Ubuntu looks a lot like Mac OS while Linux mint looks similar to Windows with it’s start menu kind of look.
Linux Mint 18 uses the Cinnamon 3.0. You can see an overview of its features in the below video .
System Requirements
Linux Mint:
512MB Ram with 1GB as recommended.
9GB of disk space with 20GB as recommended.
800 x 600 screen resolution with 1024 x 768 recommended.
Ubuntu:
512MB RAM with 2GB as recommended.
5GB of disk space with 25GB as recommended.
1024 x 768 screen resolution.
Interface
Most distros opt the standard Linux desktop interface as their default. But Both Linux Mint and Ubuntu developed their own.
Ubuntu makes use of the Unity interface. Unity Interface is a GNOME-based desktop environment that is common only to Ubuntu. To say simply, Ubuntu looks a lot like Mac OS while Linux mint looks similar to Windows with it’s start menu kind of look.
Linux Mint 18 uses the Cinnamon 3.0. You can see an overview of its features in the below video .
Both Linux Mint and Ubuntu have their own user themes. Linux has Mint-Y, while Ubuntu has Ambiance and Radiance , a new look based on the Moka and Arc theme icons.
Performance
When you consider the overall performance, Linux Mint definitely has an edge over Ubuntu when it comes to speed. Ubuntu has gotten faster over its previous versions, but Linux Mint was always pretty snappy. Even on an older and lower-powered hardware, Mint stays fast ( compared to Ubuntu). If you are installing Linux on your PC to speed it up, Mint offers you a better experience.
Conclusion
If you are someone who is installing Linux for just learning basics, Ubuntu is the one for you since it’s forum has answer to every question you ask. If you are a tech savy guy and want to dig deep into Linux but don’t know where to start, Linux Mint is your best choice. If you are installing Linux on your old PC to make it faster, Mint is again one of the best choices you have.
Sunday, October 8, 2017
10 Things You Should Delete from Facebook Immediately
Facebook is the worst.
By now, everyone knows it's just a sophisticated platform to sell you stuff.
Advertisers pay because Facebook mines your data (and simply reads what you give it willingly) for your preferences. It can sell to you better because it knows who you are.
Noone's used it earnestly as a way to connect with people since 2009.
You just scroll through photos of people you don't like enough to message personally, and watch videos, or like memes.
It's a grief pit we're all lying in, making excuses about why we haven't left yet.
So here's a few steps you can take to reduce its hold on you:
1. Delete the mobile app
Why do you need it on your phone? Seriously.
Think of all the hours you've spent scrolling. Think about the books you could have read, the people you could have met, the things you could've done in that time.
Also, Facebook grabs your location data. Which seems pointless.
The app also drains your battery massively, just by being on your phone.
Also it's got stories now.
Make the smart decision.
2. Your phone number
Firstly, why are you advertising that to your friendslist?
Secondly, Facebook just wants to be the front page of the internet, or better yet the entire internet.
Why help it along the way by supplying your personal contact information? Especially, when Facebook has made it clear it doesn't care about the welfare of your data?
3. Friends that aren't your friends
Researchers theorise that we can maintain roughly 150 stable relationships.
The odds are strong that you don't speak to most of your friendslist.
If you wouldn't stop in the street to chat, why are you keeping up the mirage online?
4. Everything Facebook knows about you for advertising
As the New Statesman covered, it's a lot.
Click this link and you'll be taken to a page which reveals your advertising preferences.
Delete everything and revoke all permissions you can.
5. Delete facial recognition
Click this link.
Go to "Who sees tag suggestions when photos that look like you are uploaded?" and revoke permissions.
6. Your location on photo tags
If you tag your location at home, people can see where you live.
This is bad for obvious reasons.
7. Your relationship status
It's a humblebrag you'll regret if and when you change to single.
8. Your status from the airport
If you post a holiday plan on social media you may not get an insurance claim accepted if you're burgled.
You told people you were away - what did you expect?
9. Your credit card details
Why would you ever do this? It seems obvious, but don't.
10. Your birthday
It can be part of a puzzle of information that is used in identity theft tests.
So why volunteer it? The birthday messages aren't worth it.
11. Your account
Honestly, burn it all down.
Wednesday, September 20, 2017
What Is “Capture The Flag” in Hacking Terms?
Learning how to defend what is yours online is one of the most important things in today’s society. The amount of cyber-attacks plaguing the world is terrifying. It’s no surprise that more individuals are relentlessly trying to further their knowledge on cyber security related tactics via training and conferences.
One of the more popular training techniques is a game dubbed “CTF” or “Capture The Flag”. CTF is a competition between security professionals and/or individuals with a passion to learn more in the cyber security world.
CTF Time defines the three most common types of Capture The Flag:
One of the more popular training techniques is a game dubbed “CTF” or “Capture The Flag”. CTF is a competition between security professionals and/or individuals with a passion to learn more in the cyber security world.
CTF Time defines the three most common types of Capture The Flag:
- Jeopardy-style CTFs has a couple of questions (tasks) in range of categories. For example, Web, Forensic, Crypto, Binary or something else. Team can gain some points for every solved task. More points for more complicated tasks usually. The next task in chain can be opened only after some team solve previous task. Then the game time is over sum of points shows you a CTF winner. Famous example of such CTF is Defcon CTF quals.
- Attack-defense CTFs is another interesting kind of competitions. Here every team has own network (or only one host) with vulnerable services. Your team has time for patching your services and developing exploits usually. So, then organizers connects participants of competition and the wargame starts! You should protect own services for defense points and hack opponents for attack points. Historically this is a first type of CTFs, everybody knows about DEF CON CTF – something like a World Cup of all other competitions.
- Mixed Competition CTFs may vary possible formats. It may be something like wargame with special time for task-based elements (like UCSB iCTF).
While hacking conferences that are constantly being held offer CTF competitions, it is more common to find CTF competitions online. With access to a training platform 24/7, CTF websites are definitely the wave of the future. Everyone with an interest in protecting their online identity and belongings should consider training with CTF.
What have you got to lose? (Besides virtually everything if you don’t learn how to protect yourself.)
Tuesday, September 19, 2017
The Top 10 Wifi Hacking Tools in Kali Linux
How to hack WiFi is second popular search after how to hack a Facebook. Most of the routers are not correctly configured and are susceptible to various kinds of attacks.
A lot of the router manufacturers and ISPs are still turning on WPS by default on their routers which makes the wireless security and penetration testing an even more important. Using the below Top 10 Wifi Hacking Tools you will be able to test your own wireless networks to find potential security issues.
1 Aircrack-ng
Aircrack is one of the very popular tools for WPA/WPA2/WEP cracking. The Aircrack-ng suite contains tools that help to capture packets and handshakes, de-authenticate connected clients and generate traffic and also tools to perform brute force and dictionary attacks. Aicrack-ng is an all-in-one suite that contains the following tools and many others:
– Aireplay-ng to generate traffic and client de-authentication
– Aircrack-ng for wireless password cracking
– Airbase-ng to configure fake access points
– Airodump-ng for packet capturing
If you wish to use this tool, make sure your Wifi card is capable of packet injection.
2 Reaver
Reaver is definitely second one in the top 10 Wifi hacking tools. Reaver is a very popular tool for hacking wireless networks. Reaver targets specifically the WPS vulnerabilities. The Reaver performs brute force attacks on WPS (Wifi Protected Setup) registrar PINs to recover the WPA2/WPS passphrase. Since there are many router manufacturers who turn on the ISPs by default, a lot of routers are vulnerable to this attack out of the box.
3 Pixiewps
PixieWPS is a new tool included in Kali Linux. Pixiewps also targets a WPS vulnerability. PixieWPS is written in C and it is used to brute force WPS PINs offline and exploits the low or non-existing entropy of vulnerable access points. This is also called a pixie dust attack. PixieWPS needs a modified version of Wifite or Reaver to work with. Considering the recent growth of this tool, itstood 3rd in our list.
4 Wifite
Wifite is an automated tool and expects a very little work form the user. When start-up it asks a few parameters to work with and then it will do all the hard work. Wifite attacks multiple wireless networks that use encryptions like with WEP/WPA/WPA2 and WPS. It captures the WPA handshakes, spoof your MAC address and safe the cracked passwords, automatically de-authenticate connected clients.
5 Wireshark
Wireshark is one of the top network security analyzing tools available online. Using Wireshark you can analyse a network to with a great detail and see what’s happening inside.
6 oclHashcat
oclHashcat is not a dedicated Wifi hacking tool and it also does not come with Kali Linux. But it can do brute force attacks and dictionary attacks on captured handshakes at a very high speeds using the raw power of GPU. Comparing to other tools like Aircrack-ng suite, oclHashcat is fast since it is using a GPU instead of a CPU. An average GPU can do upto 50,000 combinations per second with oclHashcat.
7 Fern Wifi Cracker
Fern Wifi Cracker is a wireless security auditing and attack tool and it is written in Python. It is the first tool in this list to have a graphical user interface.
8 Wash
Wash is a tool to determine whether an access point has WPS enabled or not.
9 Crunch
Crunch is a great and easy to use tool for generating custom wordlists which can be used for dictionary attacks.
10 Macchanger
Last but not least in this top 10 Wifi Hacking Tools is Macchanger. Macchanger is a little utility which can be used to spoof your MAC address to a random MAC address or you can make up your own.
What is your favorite tool?
Would you agree with our list?
Share your thoughts and suggestions in the comments section below.
Kali linux Commands
1.Command: ls
The command “ls” stands for (List Directory Contents), List the contents of the folder, be it file or folder, from which it runs. The most common options are -a (all files) and -l (long or details)
Tab completion is supported and may be configured with .inputrc
When output to file the files are listed one per line.
By default, colour is not used to distinguish types of files. That is equivalent to using –color=none.
Using the –color option without the optional WHEN argument is equivalent to using –color=always.
With –color=auto, color codes are output only if standard output is connected to a terminal (tty).
A.Command “ls -a“, list the content of folder, including hidden files the hidden files is colored blueCommand: lsblkThe “lsblk” stands for (List Block Devices), print block devices by their assigned name (but not RAM) on the standard output in a tree-like fashion.
The “lsblk -l” command list block devices in ‘list‘ structure (not tree like fashion).
Note: lsblk is very useful and easiest way to know the name of New Usb Device you just plugged in, especially when you have to deal with disk/blocks in terminal.
3. Command: sudo
he “sudo” (super user do) command allows a permitted user to execute a command as the superuser or another user, as specified by the security policy in the sudoers list.
exp: root@Kali:~# sudo add-apt-repository ppa:tualatrix/ppa
Note: sudo allows user to borrow superuser privileged, while a similar command ‘su‘ allows user to actually log in as superuser. Sudo is safer than su.
It is not advised to use sudo or su for day-to-day normal use, as it can result in serious error if accidentally you did something wrong, that’s why a very popular saying in Linux community is:
“To err is human, but to really foul up everything, you need root password.”
4. Command: mkdir
The “mkdir” (Make directory) command create a new directory with name path. However is the directory already exists, it will return an error message “cannot create folder, folder already exists”.
exp: root@Kalitut:~# mkdir Kalitut
Note: Directory can only be created inside the folder, in which the user has write permission. mkdir: cannot create directory `Kalitut‘: File exists
(Don’t confuse with file in the above output, you might remember what i said at the beginning – In Linux every file, folder, drive, command, scripts are treated as file).
5.Command: chmod
The Linux “chmod” command stands for (change file mode bits). chmod changes the file mode (permission) of each given file, folder, script, etc.. according to mode asked for.
There exist 3 types of permission on a file (folder or anything but to keep things simple we will be using file).
Read (r)=4
Write(w)=2
Execute(x)=1
So if you want to give only read permission on a file it will be assigned a value of ‘4‘, for write permission only, a value of ‘2‘ and for execute permission only, a value of ‘1‘ is to be given. For read and write permission 4+2 = ‘6‘ is to be given, ans so on.
Now permission need to be set for 3 kinds of user and usergroup. The first is owner, then usergroup and finally world.
rwxr-x–x abc.sh
Here the root’s permission is rwx (read, write and execute).
usergroup to which it belongs, is r-x (read and execute only, no write permission) and
for world is –x (only execute).
To change its permission and provide read, write and execute permission to owner, group and world.
root@Kali:~# chmod 777 abc.sh
only read and write permission to all three.
root@Kalitut:~# chmod 666 abc.sh
read, write and execute to owner and only execute to group and world.
root@Kalitut:~# chmod 711 abc.sh
Note: one of the most important command useful for sysadmin and user both. On a multi-user environment or on a server, this command comes to rescue, setting wrong permission will either makes a file inaccessible or provide unauthorized access to someone.
6.Command: tar
The “tar” command is a Tape Archive is useful in creation of archive, in a number of file format and their extraction.
root@Kali:~# tar -zxvf abc.tar.gz (Remember ‘z’ for .tar.gz)
root@Kali:~# tar -jxvf abc.tar.bz2 (Remember ‘j’ for .tar.bz2)
root@Kali:~# tar -cvf archieve.tar.gz(.bz2) /path/to/folder/abc
Note: A ‘tar.gz‘ means gzipped. ‘tar.bz2‘ is compressed with bzip which uses a better but slower compression method.
7. Command: cp
The “copy” stands for (Copy), it copies a file from one location to another location.
root@Kali:~# cp /home/user/Downloads abc.tar.gz /home/user/Desktop (Return 0 when sucess)
Note: cp is one of the most commonly used command in shell scripting and it can be used with wildcard characters (Describe in the above block), for customised and desired file copying.
8. Command: mv
The “mv” command moves a file from one location to another location.
root@Kali:~# mv /home/user/Downloads abc.tar.gz /home/user/Desktop (Return 0 when sucess)
Note: mv command can be used with wildcard characters. mv should be used with caution, as moving of system/unauthorised file may lead to security as well as breakdown of system.
9.Command: pwd
The command “pwd” (print working directory), prints the current working directory with full path name from terminal.
root@Kali:~# pwd
/home/user/Desktop
Note: This command won’t be much frequently used in scripting but it is an absolute life saver for newbie who gets lost in terminal in their early connection with nux. (Linux is most commonly referred as nux or nix).
10. Command: cd
Finally, the frequently used “cd” command stands for (change directory), it change the working directory to execute, copy, move write, read, etc. from terminal itself.
root@Kali:~# cd /home/user/Desktop
server@localhost:~$ pwd
/home/user/Desktop
Note: cd comes to rescue when switching between directories from terminal. “Cd ~” will change the working directory to user’s home directory, and is very useful if a user finds himself lost in terminal. “Cd ..” will change the working directory to parent directory (of current working directory).
File Operations:
pwd Print Name Of Current/Working Directory
The pwd is an acronym for print working directory. The pwd command is considered as one of the most frequently used commands on Linux, AIX, HP-UX, *BSD, and other UNIX like operating systems along with the ls, and cd commands. It can be used for the following purposes under Apple OS X or UNIX or Linux operating systems:
=> Find the full path to the current directory.
=> Store the full path to the current directory in the shell variable.
=> Verify the absolute path.
=> Verify the physical path i.e exclude .
cd Changing The Working Directory
cp Copy Files Or Directory
rm Remove Files And Directory
ls List Of Directory Contents
mkdir Make Directory
cat Concatenate Files And Print On Standard Output
mv Move Files
chmod Change Files Permissions
Know Your System
uname Print System Information
who Show Who Is Logged On
cal Displays Calculator
date Print System Date And Time
df Report File System Disk Space Usage
du Estimate File Space Usage
ps Displays Information Of Current Active Processes
kill Allows To Kills Process
clear Clear The Terminal Screen
cat /proc/cpuinfo Cpuinfo Display CPU Information
cat /proc/meminfo Display Memory Information
Compression
tar Store and Extract Files From An Archive File
gzip Compress Or Decompress Named Files
Network
ifconfig To Config Network Interface
ping Check Other System are reachable from The Host System
wget Download Files From Network
ssh Remote Login Program
ftp Download/Upload Files From/To Remote System
last Displays List Of Last Logged In User
telnet Used To Communicate With Another Host Using THe Telnet Protocol
Searching Files
grep Search Files(s) For Specific Text
find Search For Files In A Directory Hierarchy
locate Find Files By Name
What is pretexting?
Pretexting is defined as the action of building a planned scenario to convince a targeted victim to disclose data or make some action. It is more than only creating a trick; in some situations, it can be generating a completely new identity and then using that identity to manipulate the receipt of data.
Social engineers can use pretexting to impersonate people in specific positions and roles that they never themselves have done. Pretexting is not a one-size-fits-all solution. A social engineer must improve many various pretexts over his or her career. All of them will have one thing in common: research. Good information gathering methods can create or break a good pretext. For example, simulating the perfect tech support rep is ineffective if your victim does not use external support.
Pretexting is also used in fields of life other than social engineering. Trades; public speaking; so-called fortune tellers; neurolinguistic programming (NLP) experts; and even professors, lawyers, therapists, and the like all have to use a form of pretexting. They all have to build a scenario where people are satisfied with revealing information they regularly would not. The difference in social engineers using pretexting and others are the purposes involved. A social engineer must live that persona for a time, not just play a part.
Social engineers can use pretexting to impersonate people in specific positions and roles that they never themselves have done. Pretexting is not a one-size-fits-all solution. A social engineer must improve many various pretexts over his or her career. All of them will have one thing in common: research. Good information gathering methods can create or break a good pretext. For example, simulating the perfect tech support rep is ineffective if your victim does not use external support.
Pretexting is also used in fields of life other than social engineering. Trades; public speaking; so-called fortune tellers; neurolinguistic programming (NLP) experts; and even professors, lawyers, therapists, and the like all have to use a form of pretexting. They all have to build a scenario where people are satisfied with revealing information they regularly would not. The difference in social engineers using pretexting and others are the purposes involved. A social engineer must live that persona for a time, not just play a part.
Wednesday, September 13, 2017
What is a VPN? How does it work?
Virtual Private Networks (VPN) are used today for many reasons, in the past, these type of connections were often used in business environments when a large employer wishes to allow employees access secured internal network over the internet while working from home or in the field, but it’s becoming more and more common now to see them used by even small businesses or even individuals who for a range of reasons wish to keep their activities online secure and private.
How does it work?
when your device is trying to connect to the internet, it connects to your Internet Service Provider (ISP), which then connects your device to any website or other internet services. Your internet traffic crosses through your ISP’s servers and can be inspected by your ISP.
But when your device is using VPN, you are connecting to the VPN provider server via an encrypted connection (VPN tunnel). Once connected, all internet traffic is encrypted and secured from eavesdropping, but the VPN server can see it.
Now the first step of the security process for a VPN involves creating a tunneling protocol which acts as well a tunnel or channel for the information packets being transferred to pass through, it creates a security layer which immediately terminate the connection whenever it detects an intrusion and reconnects the client back to the server using a different route avoiding the compromised points. All of the data you’re sending and receiving in this tunnel is encrypted and secured from prying eyes.
You should use a VPN when you work on an untrusted network, which mean using your device at the coffee shops and logging in to Paypal or using your phone’s Wi-Fi to check your inbox at the airport can all potentially put you at risk.
Most frequently asked interview questions on linux
Here are some of the linux interview questions and answers that would help you to crack some of the most important and difficult interviews as a beginner.
1. What is the basic difference between Linux and Unix?
Linux is an open source operating system while Unix is a proprietary operating system. Linux is therefore, available for free to download but Unix is a paid OS (most of the versions
2. How can you find the active connections through terminal?
Using the netstat command, it is possible to find the active internet connections with the current machine. It is a command line network utility tool.
3. What is the minimum partition requirement in Linux and enlist them.
There should be minimum two partitions that every Linux distribution should have and these are as follows:
Swap Partition
Root Directory
4. What is the SU command used for in Linux?
The SU command in Linux is used to switch from one user account to another user account. You just need to type sudo su and enter the password to switch to another user account in your Linux system.
5. Tell the command to shut down the system.
The command to shutdown the OS is shutdown -h time. In place of time, you can add a number representing the seconds after which you need to shutdown the system.
6. What is fork()?
fork() is a system call primarily. It is sued to create a new process from an already active process in the system memory. Therefore, the primary process is called the parent process and the newly created process is called the child process.
7. How many run levels modes are available in Linux operating system?
There are a total of seven run level modes available in linux operating system.
8. What do you mean by Open Source System Softwares?
Open Source Softwares are the ones that are freely available for use. They generally come under the GPL License which enables us to view the source code, manipulate it and use it. However, we cannot resell them.
9. How can you list all the running programs in your Linux system?
The TOP Command can be used to enlist all the running processes in your Linux system. You can types TOP in Linux terminal and you’ll get the details of the current processes in your system.
10. What is the difference between BASH and DOS?
BASH is a Unix shell and a command language. DOS is an abbreviated form for Disk Operating System. It is used in Microsoft systems for Command Line Interface. DOS commands are not case sensitive whereas BASH commands are case sensitive.
11. How can you view the current Swap and RAM memory in your Linux system?
There is a command that can be used in the terminal in Linux operating system. The command is FREE. It enables you to view the currently active RAM and Swap memory in the system.
12. Is it legally acceptable to edit the source code of Linux Ubuntu?
Definitely Yes. Linux Ubuntu currently has a large community who regularly edits the source code for modifications and send it to the Linux team. These changes are reviewed by the core team and implemented in the next version. So, it is possible to edit the source code as it comes under GNU GPL License.
13. Which command is used to enlist the files in a particular directory?
To view the existing files in the current directory, you can use the LS command. It is an abbreviated form for LIST.
14. What is Kernel in Linux?
A Kernel in Linux is an essential part of an OS. It is the core of Linux OS. The Kernel provides basic services and interacts with the User Commands. It is fetching your commands and then retrieving the results from the OS and again sending back to the User.
15. Enlist the types of Kernels.
There are various types of Kernels listed as follows:
Monolithic Kernel
Micro Kernel
Hybrid Kernel
16. Which Program is used to securely login in Linux Operating System?
Secure Shell is used to remotely login in Linux OS. It is also known as SSH. SSH is an encrypted or cyrtographic network protocol. SSH is a good replacement of Telnet, which was previously used in Linux OS for Login purpose.
17. Name the Partition that stores the system configuration files in Linux system.
The partition that stores the system configuration files in Linux OS is /etc.
18. Who is the creator of Linux Operating System?
Linus Torvalds has created the Linux Operating System.
19. Enlist the distributions of Linux.
The different types of Linux distributions are listed as follows:
Linux Mint
Ubuntu
Mandriva
Arch
Slackware
Debian
Fedora
20. Where is the user password stored in Linux Operating System?
The User passwords are stored in the directory /etc/passwd
21. In Linux OS, which Daemon controls the Printer Spooling process.
The Line Printing Daemon, also known as LPD controls the Printer Spooling Process.
22. Enlist the filesystems supported in Linux OS.
The filesystems supported by Linux are as follows:
XFS
EXT3
NFS
RAMFS
EXT4
AUTOFS
NTFS
23. What is GNU GPL License?
The GNU General Public License is a Free Software License. This License enables the Users to share, copy, manipulate the code of the software. Therefore, the software code is available for free.
24. Which command is used to delete the files in Linux through command line?
The command used to delete the files in linux is rm.
25. Name the command used to remove the directory.
The command used to remove the directory is rmdir.
26. What should be the size of Swap memory in Linux?
Usually, the size of the Swap memory in Linux Systems should be equal or more two times that of RAM.
27. Explain SE-Linux.
SE – Linux is an abbreviated form for Security Enhanced – Linux. It has been developed to prevent Illegal Daemons and Server Misconfigurations. It provides access control implementation. It implements access authorities to daemons, programs for the files that they can access. The Security Enhanced – Linux provides Security Policy formation.
28. Who is the inventor of Unix Operating System?
The Unix Operating System is created by Dennis Ritchie and Ken Thompson at Bell Labs in 1969.
29. What is the default text editor for Linux?
The default editor for text files in Linux operating system is VI Editor. It can be used to edit any ASCII Text.
30. Name the argument to extract the files from archives using Linux Terminal.
To extract the files from archives, there can be a combination of multiple commands. If you’re trying to extract using TAR Command, then you have to use -x argument with it.
31. What is a Package Manager?
A Package Manager in Linux is a collection of softwares which provides Upgradation, Modification, Removal, Installation and Deletion of programs from the Linux Operating System. It is also known as Package Management System. It is especially developed to automatically install and update the system softwares.
32. What is the name of the Boot Loader in Linux Ubuntu Operating System?
The Boot Loader in Linux Ubuntu OS is called as GRUB Boot Loader.
33. How do you move from one directory to another directory in Linux Operating System?
By using the CD command in Linux Terminal, the user can move from one directory to another one. CD is an abbreviated form of Change Directory.
34. What is Sudo Command?
Sudo command is used to provide highest level access authority to the users. If you use a command in the Linux terminal, you may get an Access Denied output. If you want to make the terminal process a command, you can use the prefix SUDO to get administrator rights for the same.
35. What is Shell?
The Shell is basically an interface between the User Commands and the Operating System. Whatever the user types in is interpreted by the Shell and is then sent to the Operating System Kernel for fetching the results. It converts them to the System Calls.
36. Enlist boot files in Linux Operating System.
The files that are loaded a boot time in Linux OS are as follows:
/etc/fstab
/etc/init.d/rc.d/rcN.d
/boot/grub/grub.conf
/etc/initab
37. How can you find the Run – Level of Linux Operating System?
By using the runlevel command from the Linux Terminal, you can find the Run Level of your Linux system.
38. Enlist the command to install any software in Linux Ubuntu OS.
The command to install any software in Linux OS is as follows:
sudo apt install application-name
39. How can you terminate a currently executing process in Ubuntu terminal?
The key combination Ctrl + Z allows you to terminate a currently executing process in the Linux Ubuntu Terminal.
40. Which command can be used to monitor Linux ports?
The Nmap localhost command is used to monitor ports in Linux Operating Systems.
41. Enlist the Run Level Modes in Linux.
The Run Level Modes in Linux are as follows:
Halt
Reboot
Single User Mode
Undefined
Multi – User Mode
X11
Multi User Mode with Networking
42. What is the core of Linux OS?
The Linux Kernel is the core of Linux Operating System.
1. What is the basic difference between Linux and Unix?
Linux is an open source operating system while Unix is a proprietary operating system. Linux is therefore, available for free to download but Unix is a paid OS (most of the versions
2. How can you find the active connections through terminal?
Using the netstat command, it is possible to find the active internet connections with the current machine. It is a command line network utility tool.
3. What is the minimum partition requirement in Linux and enlist them.
There should be minimum two partitions that every Linux distribution should have and these are as follows:
Swap Partition
Root Directory
4. What is the SU command used for in Linux?
The SU command in Linux is used to switch from one user account to another user account. You just need to type sudo su and enter the password to switch to another user account in your Linux system.
5. Tell the command to shut down the system.
The command to shutdown the OS is shutdown -h time. In place of time, you can add a number representing the seconds after which you need to shutdown the system.
6. What is fork()?
fork() is a system call primarily. It is sued to create a new process from an already active process in the system memory. Therefore, the primary process is called the parent process and the newly created process is called the child process.
7. How many run levels modes are available in Linux operating system?
There are a total of seven run level modes available in linux operating system.
8. What do you mean by Open Source System Softwares?
Open Source Softwares are the ones that are freely available for use. They generally come under the GPL License which enables us to view the source code, manipulate it and use it. However, we cannot resell them.
9. How can you list all the running programs in your Linux system?
The TOP Command can be used to enlist all the running processes in your Linux system. You can types TOP in Linux terminal and you’ll get the details of the current processes in your system.
10. What is the difference between BASH and DOS?
BASH is a Unix shell and a command language. DOS is an abbreviated form for Disk Operating System. It is used in Microsoft systems for Command Line Interface. DOS commands are not case sensitive whereas BASH commands are case sensitive.
11. How can you view the current Swap and RAM memory in your Linux system?
There is a command that can be used in the terminal in Linux operating system. The command is FREE. It enables you to view the currently active RAM and Swap memory in the system.
12. Is it legally acceptable to edit the source code of Linux Ubuntu?
Definitely Yes. Linux Ubuntu currently has a large community who regularly edits the source code for modifications and send it to the Linux team. These changes are reviewed by the core team and implemented in the next version. So, it is possible to edit the source code as it comes under GNU GPL License.
13. Which command is used to enlist the files in a particular directory?
To view the existing files in the current directory, you can use the LS command. It is an abbreviated form for LIST.
14. What is Kernel in Linux?
A Kernel in Linux is an essential part of an OS. It is the core of Linux OS. The Kernel provides basic services and interacts with the User Commands. It is fetching your commands and then retrieving the results from the OS and again sending back to the User.
15. Enlist the types of Kernels.
There are various types of Kernels listed as follows:
Monolithic Kernel
Micro Kernel
Hybrid Kernel
16. Which Program is used to securely login in Linux Operating System?
Secure Shell is used to remotely login in Linux OS. It is also known as SSH. SSH is an encrypted or cyrtographic network protocol. SSH is a good replacement of Telnet, which was previously used in Linux OS for Login purpose.
17. Name the Partition that stores the system configuration files in Linux system.
The partition that stores the system configuration files in Linux OS is /etc.
18. Who is the creator of Linux Operating System?
Linus Torvalds has created the Linux Operating System.
19. Enlist the distributions of Linux.
The different types of Linux distributions are listed as follows:
Linux Mint
Ubuntu
Mandriva
Arch
Slackware
Debian
Fedora
20. Where is the user password stored in Linux Operating System?
The User passwords are stored in the directory /etc/passwd
21. In Linux OS, which Daemon controls the Printer Spooling process.
The Line Printing Daemon, also known as LPD controls the Printer Spooling Process.
22. Enlist the filesystems supported in Linux OS.
The filesystems supported by Linux are as follows:
XFS
EXT3
NFS
RAMFS
EXT4
AUTOFS
NTFS
23. What is GNU GPL License?
The GNU General Public License is a Free Software License. This License enables the Users to share, copy, manipulate the code of the software. Therefore, the software code is available for free.
24. Which command is used to delete the files in Linux through command line?
The command used to delete the files in linux is rm.
25. Name the command used to remove the directory.
The command used to remove the directory is rmdir.
26. What should be the size of Swap memory in Linux?
Usually, the size of the Swap memory in Linux Systems should be equal or more two times that of RAM.
27. Explain SE-Linux.
SE – Linux is an abbreviated form for Security Enhanced – Linux. It has been developed to prevent Illegal Daemons and Server Misconfigurations. It provides access control implementation. It implements access authorities to daemons, programs for the files that they can access. The Security Enhanced – Linux provides Security Policy formation.
28. Who is the inventor of Unix Operating System?
The Unix Operating System is created by Dennis Ritchie and Ken Thompson at Bell Labs in 1969.
29. What is the default text editor for Linux?
The default editor for text files in Linux operating system is VI Editor. It can be used to edit any ASCII Text.
30. Name the argument to extract the files from archives using Linux Terminal.
To extract the files from archives, there can be a combination of multiple commands. If you’re trying to extract using TAR Command, then you have to use -x argument with it.
31. What is a Package Manager?
A Package Manager in Linux is a collection of softwares which provides Upgradation, Modification, Removal, Installation and Deletion of programs from the Linux Operating System. It is also known as Package Management System. It is especially developed to automatically install and update the system softwares.
32. What is the name of the Boot Loader in Linux Ubuntu Operating System?
The Boot Loader in Linux Ubuntu OS is called as GRUB Boot Loader.
33. How do you move from one directory to another directory in Linux Operating System?
By using the CD command in Linux Terminal, the user can move from one directory to another one. CD is an abbreviated form of Change Directory.
34. What is Sudo Command?
Sudo command is used to provide highest level access authority to the users. If you use a command in the Linux terminal, you may get an Access Denied output. If you want to make the terminal process a command, you can use the prefix SUDO to get administrator rights for the same.
35. What is Shell?
The Shell is basically an interface between the User Commands and the Operating System. Whatever the user types in is interpreted by the Shell and is then sent to the Operating System Kernel for fetching the results. It converts them to the System Calls.
36. Enlist boot files in Linux Operating System.
The files that are loaded a boot time in Linux OS are as follows:
/etc/fstab
/etc/init.d/rc.d/rcN.d
/boot/grub/grub.conf
/etc/initab
37. How can you find the Run – Level of Linux Operating System?
By using the runlevel command from the Linux Terminal, you can find the Run Level of your Linux system.
38. Enlist the command to install any software in Linux Ubuntu OS.
The command to install any software in Linux OS is as follows:
sudo apt install application-name
39. How can you terminate a currently executing process in Ubuntu terminal?
The key combination Ctrl + Z allows you to terminate a currently executing process in the Linux Ubuntu Terminal.
40. Which command can be used to monitor Linux ports?
The Nmap localhost command is used to monitor ports in Linux Operating Systems.
41. Enlist the Run Level Modes in Linux.
The Run Level Modes in Linux are as follows:
Halt
Reboot
Single User Mode
Undefined
Multi – User Mode
X11
Multi User Mode with Networking
42. What is the core of Linux OS?
The Linux Kernel is the core of Linux Operating System.
How to Turn Off Your PC Using Your Smartphone
Do you want to turn off your PC at your home and save some electricity. Or may be try to shutdown your PC from outside just because it looks cool. We got you covered.
If you ever walked away from your computer and remembered that you forgot to turn it off, you can actually do it from your smart phone!
To begin with, you need to download Unified Remote app on your smartphone (iOS, Android), and you then need to download it’s server to your computer from this website right here.
You can go through the installation process on your PC and it is easy, straightforward and there is no spyware or any nonsense which comes with it. Once you are finished, make sure the server app is running on your computer, and then open the app on your mobile. It will scan for a server on your local network. Once it finds the server it will let you control your computer.
Now, the way the app works is with a bunch of different remotes. There are remotes that’ll let you control your PC as if it was a mouse and keyboard, but turning off the PC with that would be difficult if you aren’t in the room. The remote we want is called Power. Click that, and then click Shutdown or Restart to turn your PC off.
If you ever walked away from your computer and remembered that you forgot to turn it off, you can actually do it from your smart phone!
To begin with, you need to download Unified Remote app on your smartphone (iOS, Android), and you then need to download it’s server to your computer from this website right here.
You can go through the installation process on your PC and it is easy, straightforward and there is no spyware or any nonsense which comes with it. Once you are finished, make sure the server app is running on your computer, and then open the app on your mobile. It will scan for a server on your local network. Once it finds the server it will let you control your computer.
Now, the way the app works is with a bunch of different remotes. There are remotes that’ll let you control your PC as if it was a mouse and keyboard, but turning off the PC with that would be difficult if you aren’t in the room. The remote we want is called Power. Click that, and then click Shutdown or Restart to turn your PC off.
What is the deep Web?
Did you know that there’s a huge part of the internet that you can’t find simply by Googling it?
In fact, search engines can only account for about 10 % of the total internet. What is the other 90 % that’s out there? That’s what’s known as the Deep Web.
Deep Web, also known as Deepnet or the Invisible Web, the definition is quite simple, it’s the stuff on the internet that for some reasons cannot be indexed and cannot be reached by traditional search engines. It’s just any page that you simply can’t reach to without having the actual URL and the permissions to access it.
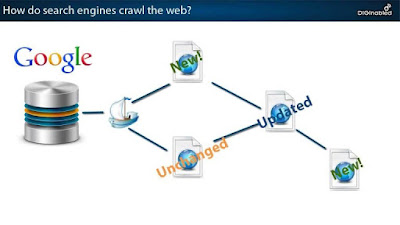
When you look for something on Google, you are actually searching an index as much of the internet as Google has been able to find. Search engines use web crawler software sometimes known as spiders to find and index web pages. They start by finding a few pages at first, then they follow links on those web pages to other web pages and so on until they have a heavy catalogue of the internet. However, there are somethings that those spiders simply can’t reach, this is the Deep Web.
There are a small subsection anonymous networks in the deep web known as the Dark Net and it uses free services such as TOR to browse the web and host websites anonymously. They also provide services that run on the internet but can only be reached through the private network, some of the services have included internet black markets such as silk road where users have to access to drugs, weapons and even assassins.
Also, Dark Web sites go down from time to time, due to their dark nature. But if you want good service, stay out of the dark!
How to Hide Files Behind an Image
We all have secret files that we don’t want anyone to look at. Most common way of hiding important files was either creating a folder inside a folder or some people change the folder type to hidden. But both of these ways are not safe and anyone with little intelligent can easily find the folder you wish to hide. Today I will show you how you can store a folder inside an image so that who ever wants to find your folder will have a really hard time finding it.
To do this a basic knowledge of command prompt is sufficient. Even if you don’t have it, I will make sure the path is easy for you to follow.
* First select an image beneath which you will hide the file you want.
* Now select the file you wish to hide and convert into .RAR formattd file using winRAR.
* Paste both of these files on the desktop.
* Now press windows key + ‘R’ and then enter cmd.
* CD stands for change directory.By typing the above mentioned command you redirect the directory to desktop.
Copy /b name.jpg + filename.rar image.jpg
Replace name.jpg with the name of image you want your file to be hidden behind. Don’t forget to add image format like .jpg,.png,.gif etc.
Replace filename with the file of your choose that you choose to hide. It must be in .rar format.
Finally Replace image.jpg with the name of the final image with files inside.
* The newly created image just looks like an image from all sides. You need to follow the following steps to extract files from images.
Accessing the Hidden File ?
To extract the file out of the image, you should open the image in winrar, which can be done in either of these ways.
* Open winrar
* Now locate your image and open it or simply drag your image in winrar.
* Extract the file and done.
To do this a basic knowledge of command prompt is sufficient. Even if you don’t have it, I will make sure the path is easy for you to follow.
* First select an image beneath which you will hide the file you want.
* Now select the file you wish to hide and convert into .RAR formattd file using winRAR.
* Paste both of these files on the desktop.
* Now press windows key + ‘R’ and then enter cmd.
* CD stands for change directory.By typing the above mentioned command you redirect the directory to desktop.
Copy /b name.jpg + filename.rar image.jpg
Replace name.jpg with the name of image you want your file to be hidden behind. Don’t forget to add image format like .jpg,.png,.gif etc.
Replace filename with the file of your choose that you choose to hide. It must be in .rar format.
Finally Replace image.jpg with the name of the final image with files inside.
* The newly created image just looks like an image from all sides. You need to follow the following steps to extract files from images.
Accessing the Hidden File ?
To extract the file out of the image, you should open the image in winrar, which can be done in either of these ways.
* Open winrar
* Now locate your image and open it or simply drag your image in winrar.
* Extract the file and done.
Autopsy – A Digital Forensic Tool
The Autopsy is a forensic tool which is used by the military, law enforcement, and corporate examiners to investigate what had happened on a smartphone or a computer.
The Autopsy has a plug-in architecture which allows the user to find add-on modules or even develop custom modules written in Java or Python.
Main features of Autopsy are:
Multi-User Cases: Collaborate with your fellow examiners on large cases.
Keyword Search: Text extraction and the index searched modules allow you to find the files which mention specific terms and find the regular expression patterns.
Timeline Analysis: Displays system events in a graphical interface to help identify activity.
Web Artefacts: Extracts web activity from common browsers to help identify user activity.
LNK File Analysis: Identifies shortcuts and accessed documents.
Email Analysis: Parses MBOX format messages, such as Thunderbird.
Registry Analysis: Uses RegRipper to identify recently accessed documents and USB devices.
EXIF: Extracts geolocation and camera information from JPEG files.
File Type Sorting: Group files by their type to find all images or documents.
Media Playback: View videos and images in the application and not require an external viewer.
Thumbnail viewer: Displays thumbnail of images to help quick view pictures.
Robust File System Analysis: Support for common file systems, including NTFS, FAT12/FAT16/FAT32/ExFAT, HFS+, ISO9660 (CD-ROM), Ext2/Ext3/Ext4, Yaffs2, and UFS from The Sleuth Kit.
Hash Set Filtering: Filter knew good files using NSRL and flags known bad files using custom hash sets in HashKeeper, md5sum, and EnCase formats.
Tags: Tag files with arbitrary tag names, such as ‘bookmark’ or ‘suspicious’, and add comments.
Unicode Strings Extraction: Extracts strings from unallocated space and unknown file types in many languages (Arabic, Chinese, Japanese, etc.).
File Type Detection based on signatures and extension mismatch detection.
Interesting Files Module will flag files and folders based on name and path.
Android Support: Extracts data from SMS, call logs, contacts, Tango, Words with Friends, and more.
DOWNLOAD AUTOPSY
Tuesday, September 5, 2017
A Review of Mobile Malware Detection Methods
Abstract—Since
the past ten years, smartphones have become widespread. These small devices are
growing rapidly with the emergence and popularity of wireless technology.
Mobile devices store personal information such as contacts and text messages. While
these devices are increasingly preferred in all ages, they are vulnerable to be
hurt by malicious codes such as viruses, worms, and so on. As the development
of functionality of these devices, the ability to get exploited by malicious activities
has also increased. The evolution of mobile malware is thought to have the same
direction as PC malware.
I.
INTRODUCTION
Mobile phones have
evolved to support multiple functions. As mobile phone functionality improves, the
ability to get exploited by malicious activities has also increased. For
various services such as social networking and games provided from smartphones
with the help of 3rd party applications, these are released to
obtain sensitive information from mobile devices. There are many kind of
smartphone OSs in the world. The most popular one is Android. Any Third-party
vendors can create applications for running on Android devices and put them on
the app market such as Play store. In some cases, even a trusted application
can share the user's information to others without its consent. The evolution
of malware on mobile devices is widely considered to have the same direction as
PC malware evolution. Mobile devices incorporate a variety of wireless
communication methods, which make it easy to connect, making it a simple target
for malware. Like Computers (PC), the mobile devices can access the Internet for
web browsing and emails. It also has a function to communicate with WLAN, SMS/MMS,
Bluetooth connection. It’s most important and interesting reason to believe
that attackers use mobile devices since its way more popular among the users. However,
with the help of technology and detection algorithms for development, special attention is needed to protect these network
devices from malware.
II.
Research Objectives
Due to the
expansion of mobile devices in the world, the no of malware attacking mobile
devices is also increasing. special attention is needed to protect these devices
from malware. There are many types of threats on mobile devices. Some of them
will be described in the section III. In addition to that, the history of
mobile threats will be discussed. Many researchers have done various kind of
researches regarding to that particular topic. In the section IV, a review of
that publications will be discussed.
III.
Definitions and Categories
A.
Types of Attacks
The work by Dagon et al. [1] has been
examined the attacks types. These attacks types have been listed below.
Table 1: Types of Mobile Attacks
Security Goals
|
Attacks Types
|
Confidentiality
|
Theft of data, blue-bugging, blue-snarfing
|
Integrity
|
Mobile-hijacking
|
Availability
|
Denial-of-service and battery draining
|
1)
Theft of data
It is an act of stealing
information stored on a computer, server, or other device from an unknown
victim, infringing privacy or obtaining confidential information. Attackers
always try to obtain dynamic and static information. Dynamic information contains
location data, power usage, and other sensitive data, that the device does not
usually capture [1]. Static information contains data that mobile devices store
or send over the network. The blue-snarfing and blue-bugging attacks are examples
of theft of data. The blue-bugging attack gives unauthorized access to the mobile
phone and spies phone calls. However, this attack has moved along to being able
to control/move around/mislead the different functions of the phone [1]. Blue-snarfing
attack is unauthorized access and data retrieval from applications.
2)
Denial-of-Service (DoS)
DoS can be done by
flooding unusual traffic to the device. And also it can be done by draining the
power or performance of the mobile devices. Now, it is very easy to crash most
Bluetooth applications on mobile devices by sending useful packets, corrupted
packets and wrong file formats repeat. DoS is a major attack type that can be
exploited known vulnerabilities [2].
3)
Mobile-hijacking
Some harmful programs or
apps tries to use the victim's mobile resources. Pilfered duplicates of PC
recreations were contaminated with infections that sent costly SMS messages
when clients played unlawful duplicates. Hijacking phone resources are not
unexpected.
B.
Threats on Mobile Devices
These are
malicious software targeting mobile phones and wireless compatible PDA, causing
system collapse and loss or leakage of confidential information by means of WLAN
Bluetooth, SMS/MMS. There are various assault vectors, undermining the security
of cell phones. There are three main types of attacks: malware attacks,
grayware attacks, spyware attacks.
1)
Malware
This type of
attack steals the sensitive information of mobile devices. And also these
attacks can damage the devices [22]. If the device is vulnerable and tricks the
user to install unwanted applications that the attacker can get the device root
access. There are many types of malware. Several attacks are shown below.
a)
SMS attacks
In SMS attacks,
an attacker can advertise and disseminate phishing links. An attacker can also
exploit vulnerabilities by using SMS messages [22].
b)
Bluetooth attacks
In Bluetooth
attacks, an attacker can steal victim sensitive data from the device, and track
the mobile location. With Blue-bugging, an attacker can launch software
containing malicious activity and listen to conversations [22].
c)
Phone jail-breaking
With
jail-breaking, an attacker can remove the effect on the security of the operating
system and it allows to install applications without additional signatures on
the OS. It attracts users to take advantage of additional features [22].
d)
Premium rate attacks
The premium rate service can deliver
valuable useful content to the mobile devices. Users can receive information
about financial, technical support, or adult services When used in a legitimate
way [22].
2)
Spyware
Spyware is
another type of attack that is installed on a computer or mobile devices without
knowledge of the owner and collects the owner's personal information. By
installing applications without user permissions, spywares can access the
device physically. By collecting information about the victim's phone, it is
sent to the attacker.
3)
Grayware
Graywares are
applications that act in a way that is irritating or undesirable. Most
probably, grayware collects the data from mobile devices for marketing
purposes. Their goal is not to hurt clients but rather to trouble them.
C.
Attacks on Mobile Devices
Looking at the history
of attacks, many Trojan horses, worms and viruses have entered the mobile world
and are being influenced. Well known examples for some threats on Symbian-based
smart phones include Cabir, Skull and Mabir [1]. Many of these variants viruses
strengthen the attack and reveal unexpected and unexpected levels of exposure.
According to McAfee 2008, mobile security report, almost 14% of worldwide
versatile clients had been specifically tainted or had known somebody who was
contaminated by a portable infection. The one of the key characteristics that
differentiate threat actors is Motivation. Despite the fact that not each actor
needs to take information amid each battle to fulfill a goal, many crusades
require it. Figure 1 below describes the motivations of threat actors [3].
State-based entities
generally try to gain strategic advantage, but it often targets intellectual
property rights. The financial goal of an organized criminal makes it easy to
understand its motivation. It tends to focus on large credit cards, banking
transactions, or personally identifiable information.
Hacktivists are probably
the hardest to stop, as internal data can affect the reputation of the
organization.
Most of, Much of
security breaches in past years have been easily detectable. They were complex
with arranging, focusing on, stalking and running. According to the McAfee et al.
[3], a change during the past two years, with a significant increase in the
number of technically sophisticated attacks has been identified. It looks like
fragmentary invasion, but it is hiding in inactive code, waiting for an
unprotected moment. These threats avoid signature-based ancestor traps, changes
by new deployment using encryption and dynamic code changes, and prevent data
corruption.
Since the popularity of
Android OS, the possibility of being vulnerable is at higher level. The malware
called Slocker rose to become a more prominent threat in 2015 [4]. Slocker's
growing popularity indicates that mobile malware targets content stored on the
device.
If one malicious program
shares another code or behavioral feature, it is usually considered to belong
to the same family.
Individual threats of
malware families are often detected by security software and identify the
essential characteristics of families. Figure 3 describes top ten android
malwares in 2015 and the things that they are going to do according to the F-Secure
Threat Report 2015.
D. Approaches in Malware Detection
Malware needs to
be analyzed to understand the risks associated with malwares. In order to
clarify the behavior and function of malware, many detection methods exist in
the literature. In recent years, interest in malware detection technology of
mobile devices has increased. Three main approaches were considered.
1)
Static analysis
Static analysis
inspects software properties and source code to investigate downloaded app. However,
software encryption technology makes static analysis difficult. Static analysis
is further divided into two categories.
a)
Signature-based detection
Signature-based
detection uses specific patterns such as byte sequences or known malicious
instruction sequences to detect attacks. In this detection method, the detected
patterns are referred as signatures [5]. Signature detection can identify malicious
activities before infecting.
b) behavior-based detection
This is another
general technique that looks for abnormal behavior based on the operation
checker resident in memory. In this matter, the user is alerted. Behavior
checkers have the disadvantage that some changes have been made to the system
before malicious activity is detected.
2)
Dynamic analysis
Dynamic analysis
runs the application in a different environment and tracks its execution
behavior. Dynamic analysis can be used to reveal the natural behavior of
malware when the executed code is analyzed. Therefore, it is not affected by
obfuscation attempt.
3)
Integrity Checking
Integrity checking uses a log of all files
existing in the system. The log contains information of files such as file
size, timestamp, checksum, etc. Each time the integrity checker runs, the files
on the system are checked and compared with previously saved characteristics.
IV.
Review Of The Literature
Some relevant related work that includes the
above-mentioned malware detection techniques will be presented and reviewed.
D.Venugopal et al.
[5], has described a method of representing signatures for detecting viruses in
mobile devices. In this, the hash table is used to store hash values of virus
signature for fast matching. The first matching signature cut was used to speed
up that process. This represents a part that is unlikely to occur in a regular
file before matching the whole signature. Nokia 6682 device running on Symbian
OS was used to test this method. As a result, this method was 98% faster than
the sequential scan. Using this method, new malware which completely different
from the previous malware cannot be detected. To improve the detection, this
method needs to be combined with more sophisticated malware detection methods
such as heuristic scanning and detection. As the virus evolved, the technology
to protect the virus had to evolve. The detection of malicious code in this
context includes more sophisticated approaches such as heuristics and behavior
analyzers [6].
D. Venugopal, G.
Hu, and N. Roman et al. [7], have described a method that is different to the
previous. In there an intelligent heuristic method is used to detect viruses in
the mobile devices. It uses Dynamic Link Libraries (DLLs) to detection. The
virus uses the list of DLL functions to indicate the nature of the virus on
that function. With this approach, new viruses can be detected. According to
the research, Symbian-OS is used to test this method, and for non-virus
programs, it has got 95% detection rate and 0 false detection rate for all
viruses.
F. Peters, A. Shmidt,
S.Albayrak and F.Lamour et al. [8], describe a machine learning algorithm for
detecting malicious activity of mobile devices such as smartphones. A remote
anomaly detection system performs anomaly detection. Each smartphone behaves as
a client and sends a series of functions pulled out by studying different resources
measurements, hardware and software to the remote anomaly detection system.
These functions are stored in the database. The detection components access the
database to analyze malicious activity data. Using Symbian-OS and Windows
Mobile, this method has been tested. As a result, there are disk space savings,
computational and communication cost savings, and positive impact on battery
life.
Kim at el. [9] has
shown a Proposal of a framework for detecting and monitoring threats of energy
greed by constructing power usage from gathered instances. After generating the
power signatures, the signatures available in the database is compared by the data
analyzer. Batyuk et al. [10] proposed a system for static analysis of android
applications. Next, the method is developed by overcoming the security threat
introduced by the application and disabling malicious functionality. Ontang et
al. [11] proposed a secure application interaction framework. It works by increasing
the architecture of android security for protection of interfaces and raising
interaction policies.
J. Cheng et al.
[12] presented a behavior checking system for smart phone called SmartSiren that
consists of cooperative virus detection and alert system. On each smartphone,
there is a system that running a light-weight agent. The agent tracks
communication activity on the device and periodically reports the summary of
these activities to the proxy. A centralized proxy is used to assist the virus
detection and alert processes. The proxy collaboratively analyzes the reports
received and identifies single-device or system-wide virus manner. When a
potential virus is detected, the proxy sends an alert to both the infected
device and a subset of the infected device (which may be in direct contact with
the infected device). As a result, SmartSiren prevents wide area virus
outbreaks. A better result can be obtained by using this method instead of
using signature based detection.
Bose et al. [13]
presented a behavioral detection framework. It works in a way of representing
the malware behavior. It discovers applications actions logical order to do
that. Malicious behavior is distinguished from normal behavior by training the
SVM. The system is evaluated with an accuracy of 96% for both real world and
pseudo mobile malware.
The method
called pBMDS based on behavior-based malware detection has been described by L.
Xie et al. [14]. It uses an approach that is probabilistic by matching user
inputs with system calls to detect distrustful activities in mobile phones. It
observes the specific behavior of mobile phone applications and operations
users on input and output constrained devices. Hidden markov model(HMM) is
leveraged to learn user-behavior and malware behavior for discrimination of
differences between them. As a result, pBMDS was shown to be effective,
lightweight, easy to deploy, and capable of detecting unknown malware.
Wei et al. [15]
proposed a static feature-based approach and developed a system called Droid
Mat that can detect and distinguish android malwares. Their mechanisms consider
the static information characterizing android malware about access permissions,
intents, and components, and apply a clustering algorithm to enhance malware
modeling capabilities. Finally, DroidMat is efficient as it can predict 1738
applications in half the time compared to Androguard, a well-known tool
published in Blackhat 2011.
Enck et al. [16],
proposed Apps-playground framework for automatic dynamic analysis of android
applications. This allows to analyze malicious applications as well as
applications that leak personal data from smartphones without user consent. For
dynamic analysis, a detection technique including a function of searching
application code as much as possible is necessary, and the environment must be
realistic to the extent that a malicious application cannot be obfuscated.
Automated analysis code effectively explores applications by integrating
discovery. Detection technology detects malicious functionality while running
applications. It includes suspicious traces that monitor TaintDroid’s
confidential information APIs, such as the SMS API, and perform kernel-level
monitoring for tracing of root exploits. Automatic exploration techniques are
useful for code coverage of applications by simulating events. For automatic
discovery of android applications, intelligent black box execution tests and
Fuzzy tests are used. Disguise technology creates a realistic environment by
providing data such as IMEI, contacts, SMS, GPS coordinates etc.
An Android
application sandbox (AA sandbox) system was proposed by T. Blasing et al. [17] for
analysis of android application consists of high speed static pre-check
function and kernel space sandbox. Static analysis and dynamic analysis are used
to perform distrustful application detection in the android application. AA Sandbox
takes APK file and find out following files by decompressing
them-Androidmanifest.xml, res/, classes.dex.
Security
permissions and application descriptions are contained in the manifest file. The
Res/ folder defines the layout, the graphical user interface (GUI) element and the
language of the application. The Classes.dex file includes runnable program code
to run on the dalvik VM. This code is compiled into a Java file using baksmali
and it searches for suspicious code patterns. Monkey program is created for
application stress testing. These monkey programs generate a pseudo-random sequence
of user events. This is used for hijacking logging operation system calls and
is useful for obtaining application logging behavior at the system level. For
testing purposes, approximately 150 applications are gathered [17].
A dynamic
analysis system supported runtime behavior for android applications has been
presented by L. X. Min and Q. H. Cao et al. [18]. That system includes event
detector, log monitor and parser. Event triggers can use static analysis to
simulate user behavior. The static analyzer gets the support of the application
.apk file and generates manifest.xml and java code. Semantic analysis retrieves
a list of risk-based permissions, activities, and services, including other
information such as hash codes and package names. A control flow graph (CFG) about
an application is generated by dataflow analysis [18]. It uses a way of mapping
user-defined methods and API calls to do that. Confidential information on
applications can be obtained by executing applications with customized emulators
using loadable LKM. In the log recorded by the debug tool logcat, highly
confidential operation is sent to the log parser. The log monitor analyzes the
log data by collecting log data while the application is running. The parser
analyzes the log data by extracting confidential information and filtering
unnecessary information. 82 of 350 apps that were got from Amazon Android
market showed that they leak the user’s private sensitive data [18].
The authors mentioned
a method called Paranoid Android [19]. It uses remote security servers which
has exact copy of the mobile phones in virtual environment. It is for checking the security of smart
phones. Because the server is not subject to the same constraints as smart
phones, multiple detection methods can be applied simultaneously. The execution
of the phone is recorded and played on the security server in the cloud. Paranoid
Android uses a warning mechanism to warn the user about the malicious activity
that is going to be happen, when an attack is detected. If the device is already
sieged by the attack, it can be returned to. Using an Android mobile phone, the
prototype of Paranoid Android was tested [19]. As a result, even during the
high activity period, the transmission overhead is maintained at 2.5 Kbps or
less, the idle period is shortened, and the battery life is shortened by about
30%.
A framework for
a background monitoring system is described by M. Becher and F.C. Freiling et
al. [20]. It works by collecting the software to be installed by the user on
the device and automatically perform a dynamic analysis of the software. The
analysis system uses mobile networks as analysis locations rather than mobile
devices for two reasons. First, mobile networks have more computing power to carry
out more thorough analysis. Second, since it is easier to handle compared to
handling local connections, it is pretended that mobile network will deliver
the most software. Therefore, suspicious manner in the mobile network is analyzed
by software before the user installs the software on the mobile device. The automatic
dynamic analysis where system calls are recorded and malicious acts are
analyzed helps to do that. There are three stages that dynamic analysis is
done. In the first stage, the software components are collected. In the second
stage, we collected samples are analyzed with specific modules called mobile sandboxes.
This method is similar to the process described by T. Blasing [17]. This module
runs the sample in an environment where steps of the examined sample can be
watched. This will result in a series of API calls used during program
execution. The third step is providing a response to the analysis. When
malicious activity is detected the installation of the software can be rejected
by mobile network operators. It also might send a message to alert the user
that the program violates the user’s or network’s security profile.
In additions to
these methods, an architecture for automatic downloading of android
applications from the android market has been proposed by R. Johnson, Z. Wang,
C. Gagnon et al. [21]. Various algorithms used to search applications, such as
downloading applications by application category. With static analysis, required
permissions can be obtained based on its functionality. The authorization name
is searched in the Android source code and mapped in the API call to see if the
requested access right is correct. The program examines all the files of the
application and gets a list of method calls used by the application. Each
method call is then compared with the method calls listed in the permission
protected Android API call to find the exact permissions. The similarities and
differences are identified in the restricted permission set by comparing them with
all the permissions nominated in the AndroidManifest.xml file [21], no
additional permissions, no access rights, and no permission set required for the
function.
V. FUTURE RESEARCH
The threat
associated with mobile malware is expanding due to the expansion of mobile
devices all over the world. New malicious mobile programs are introduced daily
with the incrementing of the mobile technologies. Mobile devices are the
majority of our daily lives, Connecting us to social media, banking, videos,
gaming, online shopping etc. Therefore, preventing of those mobile threats are
highly recommended. In the review, the history and the current state of mobile
malware detection techniques have been discussed. The future of mobile malware
and detection techniques should be talked to make the future better.
In the review,
it was shown that anomaly detection is mainly performed by a proxy that is off
from the attack source. This type of detection concept has two main advantages.
First, a large processing speed and power usage are required by the large-scale
detection solutions. Second, as the reactive approach is always better than
being aggressive, the proxy can inform other users of potential attacks before
the entire network is involved in malware activity. Because reactive approach
is always better than proactive. Based on the outline of a quickly changing
attack, there is no way to specify one method for the future of virus
detection. The thing that is required is an efficient malicious activity
detection method. The spread rate can be reduced by it and also could be
applied at network level to protect the spreading through network routes. It
seems that there is a high possibility that the malicious code detection
technology that will appear in the future will be essentially distributed. It
is thought that focus will shift from endpoint protection to network-wide
protection. There are several recommendations for designing algorithms to
detect mobile-based applications including malware. These are:
To build a
feature set that detects mobile malware, multiple feature extraction sources
are needed.
In order for
developers to recognize vulnerabilities related to mobile malware, domestic and
foreign databases are required to report malware incidents.
Machine
communication and authentication tools must be used across multiple device
platforms.
To improve the detection
rate, an artificial intelligence algorithm should be used.
This review
forms the foundation for future work on mobile malware detection. It has also
established the framework of investigation necessary to advance towards the
development of the network-wide protection framework.
VI. Conclusion
Smartphones are becoming increasingly popular in positions of power, sensors and communication. Modern smartphones offer many services such as messaging, Internet browsing, e-mail transmission, games etc. in addition to traditional voice services. Because of its multifunctionality, new security threats are emerging in mobile devices. This paper is a review of malware detection techniques for mobile devices. Additionally, the history and current situation of mobile threats and vulnerabilities have been discussed in this paper. Problems related to traditional signature-based detection methods are also highlighted. Various mobile malware detection methods were described. This paper provides sufficient literature for the researchers on the mobile malware detection methods and hope that it will motivate the researchers and practitioners to examine mobile security issues and its applications.
Acknowledgment
This work very
well supported in part of all the authors who has shared their knowledge along
with their researches mentioned in the below. And we thank our supervisor who
in charge of this module Mr.Amila Nuwan Senarathne who guided us throughout the
semester.
References
[1] D.
Dagon,T. Martin, and T. Starner, “Mobile Phones
as Computing Devices, the Viruses are Coming!,” Pervasive
Computing, IEEE, vol. 3, no. 4, Oct-Dec.
2004, pp. 11-15.
[2] Q. Yang, R.
H. Deng, Y. Li, and T.Li, “On the Potential of Limitation-oriented Malware Detection and
Prevention Techniques on Mobile
Phones,” International Journal
of Security and
its Applications, vol. 4, no. 1, Jan. 2010.
[3] McAfee
Labs. “McAfee Labs Threats Report”, August 2015.
[4] F-Secure.
“Threat Report”, 2015.
[5] D. Venugopal, “An Efficient Signature Representation
and Matching Method for Mobile Devices,” Proc.
2nd Annual International workshop on Wireless Internet (WICON
’06), Boston, MA, United States, 2006.
[6] A.
Shevchenko, “Malicious Code Detection Technologies,” Kaspersky Lab, Inc.2008.
[Online]. Available: https://pdfs.semanticscholar.org/36a6/675b54a963aa4cba708882f1e172536a5dba.pdf
[7] D.
Venugopal, G. Hu, and N. Roman, “Intelligent Virus Detection on Mobile
Devices,” Proc. International Conference on Privacy, Security and Trust: Bridge
the Gap between PST Technologies and Business Services (PST’06), Ontario,
Canada, 2006, pp.1-4.
[8] A. Shmidt, F. Peters, F. Lamour, and S. Albayrak,
“Monitoring Smartphones for Anomaly Detection,” Proc. 1st International
Conference on MOBILe Wireless MiddleWARE, Operating Systems, and Applications,
2008.
[9] H.Kim,
J.Smith, K.G.Shin, “Detecting energy-greedy anomalies and mobile malware
variants”, Proceedings of the 6th international conference on Mobile systems,
applications, and services, pp.239-252.ACM, 2008.
[10] L.
Batyuk, M. Herpich, S. A. Camtepe, K. Raddatz, A. D. Schmidt and S. Albayrak, “Using
static analysis for automatic assessment and mitigation of unwanted and
malicious activities within Android applications,” 2011 6th International
Conference on Malicious and Unwanted Software, Fajardo, 2011, pp. 66-72.
[11] M.Ongtang,
S.E.McLaughlin, W.Enck, P.D.McDaniel, “Semantically rich application-centric security in
android”, In Proceedings of
the 25th Annual Computer
Security Application Conference (ACSAC), pp.340-349, 2009.
[12] J.
Cheng, S. Wong, S. H. Y. Wong, H. Yang, and S. Lu, “Smart Siren: Virus
Detection and Alert for Smartphones,” Proc. 5th International
Conference on Mobile Systems, Applications and Services (MobiSys ‘07), San
Juan, Puerto Rico, pp. 258-271, 2007.
[13] A.
Bose, X. Hu, K.G.Shin, T.Park, “Behavioral detection of malware on mobile
handsets”, In MobiSys ’08, Proceeding of the 6th international conference on Mobile systems, applications, and
services, pp.225-238, ACM, New York, 2008.
[14] L.
Xie, X. Zhang, J. Seifert, and S. Zhu, “pBMDS: A Behavior-based Malware
Detection System for Cellphone Devices,” Proc. Third ACM Conference on wireless
Network Security (WiSec’10), Hoboken, New Jersy, USA, 2010.
[15] D.
J. Wu, C. H. Mao, T. E. Wei, H. M. Lee and K. P. Wu, “DroidMat: Android Malware
Detection through Manifest and API Calls Tracing,” 2012 Seventh Asia Joint
Conference on Information Security, Tokyo, 2012, pp. 62-69.
[16] V.
Rastogi, Y. Chen, W. Enck, “AppsPlayground: Automatic Security Analysis of
Smartphone Applications”, In CODASPY'13
Proceedings of the third ACM
conference on Data and application security and privacy, pp.209-220. ACM, 2013.
[17] T.
Bläsing, L. Batyuk, A. D. Schmidt, S. A. Camtepe and S. Albayrak, “An Android
Application Sandbox system for suspicious software detection,” 2010 5th
International Conference on Malicious and Unwanted Software, Nancy, Lorraine,
2010, pp. 55-62.
[18] L.
X. Min, Q. H. Cao, "Runtime-Based Behavior Dynamic Analysis System for
Android Malware Detection", Advanced Materials Research, Vols. 756-759,
pp. 2220-2225, 2013.
[19] G.
Portokalidis, P. Homburg, K. Anagnostakis, and H. Bos, “Paranoid Android: Versatile Protection for Smartphones,” Proc. 26th
Annual Computer Security Applications Conference (ACSAC’10), Austin, Texas,
USA, pp. 347-356, Dec. 6-10, 2010.
[20] M.
Becher and F.C. Freiling, “Towards Dynamic Malware Analysis to Increase Mobile
Device Security,” Proc. SICHERHEIT, pp. 423-433,
2008.
[21] R. Johnson, Z. Wang, C. Gagnon and A. Stavrou, “Analysis
of Android Applications' Permissions,” 2012 IEEE Sixth International Conference
on Software Security and Reliability Companion, Gaithersburg, MD, 2012, pp.
45-46.
[22] D.
Stites, A. Tadimla “A Survey of Mobile Device Security: Threats,
Vulnerabilities and Defenses”, 2011. [Online]. Available: http://afewguyscoding.com/2011/12/survey-mobile-device-security-threats-vulnerabilities-defenses/
Subscribe to:
Comments (Atom)
Get Unlimited Free Trials Using a "Real" Fake Credit Card Number
When I see the words "free trial," I know I'm probably going to have to whip out my credit card and enter in the number to ...

-
What is Bitcoin? Bitcoin is a cryptocurrency and a digital payment system created by an unknown programmer, or a group of programmers, u...
-
When I see the words "free trial," I know I'm probably going to have to whip out my credit card and enter in the number to ...